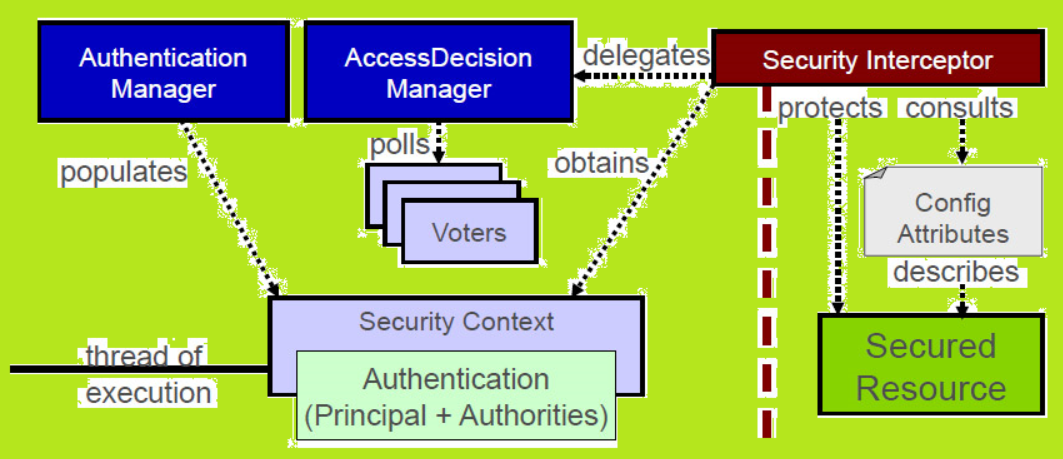
Spring security architecture diagram
Spring Security Authentication
Spring security provides AuthenticationManager interface for authentication process. It has only one method.
public interface AuthenticationManager {
Authentication authenticate(Authentication authentication) throws AuthenticationException;
}
The authenticate() method can return an Authentication if the input represents a valid principal. Normally it returns authenticated=truefor the above mention case. It will throw an AuthenticationException if the input represents an invalid principal. It will return null if it can’t decide whether the input value is valid or invalid.
The ProviderManager is the most common implementation of AuthenticationManager. It delegates to a chain of AuthenticationProvider objects. It has an optional parent. It can consult to it if all providers return null. AuthenticationException will be thrown if no parent is available.
AuthenticationProvider is like an AuthenticationManager only difference is that it has an extra method. This extra method allow the caller to query if it supports a given Authentication type.
public interface AuthenticationProvider {
Authentication authenticate(Authentication authentication)
throws AuthenticationException;
boolean supports(Class<?> authentication);
}
Note: In an application we may have logical groups of protected resources. For example all web resources that match a path pattern /app/**. In such situations each group can have its own dedicated AuthenticationManager. These dedicated AuthenticationManager instances can share a common parent which will act like a global resource.
Spring security framework provides the facility to customize the Authentication Managers with the help of AuthenticationManagerBuilder.
@Configuration
public class ApplicationSecurity extends WebSecurityConfigurerAdapter {
// Our code statements
@Autowired
public initialize(AuthenticationManagerBuilder builder, DataSource dataSource) {
builder.jdbcAuthentication().dataSource(dataSource).withUser("jai")
.password("unknown").roles("USER");
}
}
Note: Spring boot comes with a default global AuthenticationManager which is secure enough on its own. We can replace it by providing your own bean of type AuthenticationManager.
Spring Security Authorization or Access Control
Authorization process starts when authentication process completes. AccessDecisionManager interface is the core entity in the authorization process. Spring security framework provides three implementations of AccessDecisionManager interface and all three delegate to a chain of AccessDecisionVoter.
The AccessDecisionVoter takes an Authentication and a secure Object. The secure Object has been decorated with ConfigAttribute.
boolean supports(ConfigAttribute attribute);
boolean supports(Class<?> clazz);
int vote(Authentication authentication, S object,
Collection attributes);
A ConfigAttribute represents a metadata for secure object. This metadata determine the level of permission required to access it. ConfigAttribute can be like name of user role.
Web Security
Spring security uses servlet filters to provide the web security. Servlet filters are the objects which are used to perform some filtering task. Spring security provides FilterChainProxy interface to perform web security.
Note: Spring Boot application uses the security filter as a @Bean in the ApplicationContext. It is applied to the all requests by default. Default position where this default filter will install is SecurityProperties.DEFAULT_FILTER_ORDER.
Method Security
Spring security also provide the feature of method security i.e. it provides the support for applying access rules to Java method executions. To allow method security, we have to enable method security. Normally, we do it on top level or module level configuration for our app. For a secure method, caller have to go through with the security check first. If caller satisfy the check, method will execute otherwise caller will get AccessDeniedException.
@Service
public class TestService {
@Secured("ROLE_USER")
public String secureMethod() {
return "Hello Method Security";
}
}